Linux Network Namespaces
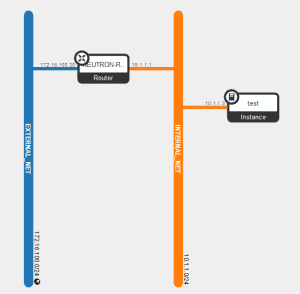
The Linux Network Namespace (netns) is a feature within the 2.6.27+ Linux kernel. Normally a Linux process will run within a network namespace. By default this is inherited from its parent process. Network namespaces allow for the process to run within a different network namespace. This allows for virtual instances of the Linux network stack … Read more