How do I Create an SSL VPN on a Check Point Gateway ?
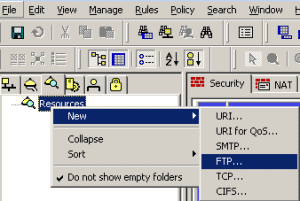
Below shows you the steps in order to create an SSL VPN on a Check Point Gateway : Create a new network object. This will be used as the remote users IP address. Name this “net_office-mode-IPs” Within the Check Point Object under Tolopogy > VPN Domain add your local domain. Within the Check Point Object … Read more