Check Point – Ive pushed the Wrong Policy
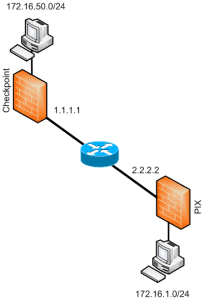
Issue There may be a time where you install the wrong policy onto a Check Point Firewall. This can block your connections, and screw which traffic is allowed through the firewall. Resolution These steps will show you how to remove and reinstall the correct policy via the CLI on the manager (SCS), 1. First of … Read more